Can we trust blockchains?
Maryline Laurent, Télécom SudParis – Institut Mines-Télécom, Université Paris-Saclay
[divider style=”normal” top=”20″ bottom=”20″]
[dropcap]B[/dropcap]lockchains were initially presented as a very innovative technology with great promise in terms of trust. But is this really the case? Recent events, such as the hacking of the Parity wallet ($30 million US) or the Tether firm ($31 million US) have raised doubts.
This article provides an overview of the main elements outlined in Chapter 11 of the book, Signes de confiance : l’impact des labels sur la gestion des données personnelles (Signs of trust: the impact of seals on personal data management) produced by the Personal Data Values and Policies Chair of which Télécom SudParis is the co-founder. The book may be downloaded from the chair’s website. This article focuses exclusively on public blockchains.
Understanding the technology:
A blockchain can traditionally be equated to a “big,” accessible and auditable account ledger deployed on the internet network. It relies on a large number of IT resources spread out around the world, called “nodes,” which help make the blockchain work. In the case of a public blockchain, everyone can contribute, as long as they have a powerful enough computer to execute the associated code.
Executing the code implies acceptance of the blockchain’s governance rules. These contributors are responsible for collecting transactions made by blockchain customers, aggregating transactions in a structure called a “block” (of transactions) and validating the blocks before they are linked to the blockchain. The resulting blockchain can be up to several hundred gigabytes and is duplicated a great number of times on the internet, which ensures wide availability of the blockchain.
Elements of trust
The blockchain is based on the following major conceptual principles, naturally positioning it as an ideal technology of trust:
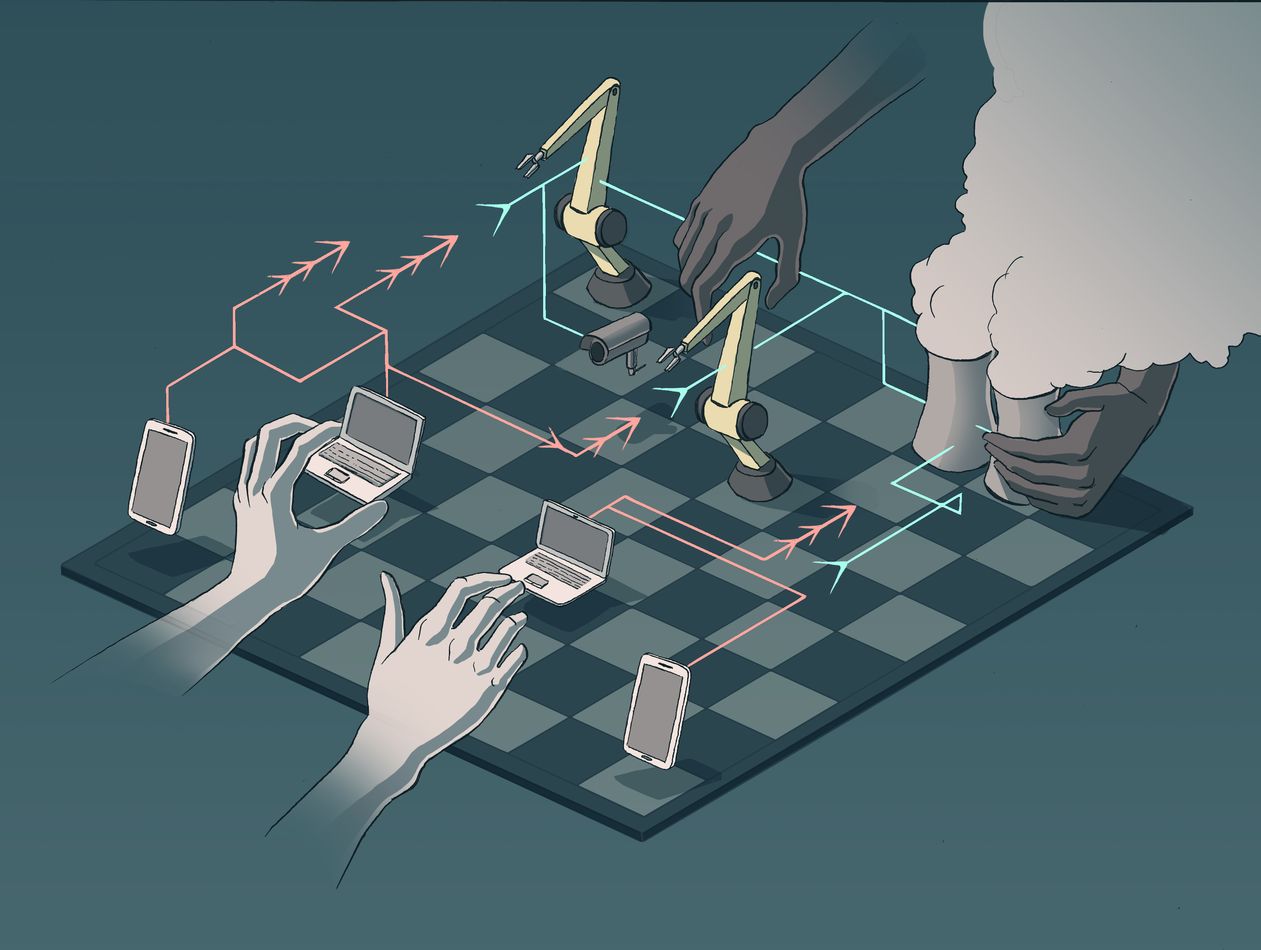
- Decentralized architecture and neutrality of governance based on the principle of consensus: it relies on a great number of independent contributors, making it decentralized by definition. This means that unlike a centralized architecture where decisions can be made unilaterally, a consensus must be reached, or a party must manage to control over 50% of the blockchain’s computing power (computer resources) to have an effect on the system. Therefore, any change in the governance rules must previously have been approved by consensus between the contributors, who must then update the software code executed.
- Transparency of algorithms makes for better auditability: all transactions, all blocks, and all governance rules are freely accessible and can be read by everyone. This means that anyone can audit the system to ensure the correct operation of the blockchain and legitimacy of the transactions. The advantage is that experts in the community of users may closely examine the code and report anything that seems suspicious. Trust is therefore based on whistleblowers.
- Secure underlying technology: Cryptographic techniques and terms of use guarantee that the blockchain cannot be altered, that the transactions recorded are authentic, even if they have been made under a pseudonym and that blockchain security is able to keep up with technological advances thanks to an adaptive security level.
Questions remain
Now we will take a look at blockchains in practice and discuss certain events that have raised doubts about this technology:
- A 51% attack: Several organizations that contribute significantly to running a blockchain can join forces in order to possess at least 51% of the blockchain’s computing power between them. For example, China is known to concentrate a large part of its computing power — a total of two thirds of its computing power in 2017 — in the bitcoin blockchain. This raises questions about the distributed character of the blockchain and the neutrality of governance since it results in completely uneven decision-making power. Indeed, majority organizations can censure transactions, which impacts the blockchain’s history, or worse still, they can have considerable power to get governance rules that they have decided upon approved.
- Hard fork: When new governance rules that are incompatible with previous ones are brought forward in the blockchain, this leads to a “hard fork,” meaning a permanent change in the blockchain, which requires a broad consensus amongst the blockchain contributors for the new blockchain rules to be accepted. If a consensus is not reached, the blockchain forks, resulting in the simultaneous existence of two blockchains, one that operates according to the previous rules and the other, according to the new rules. This forking of the chain undermines the credibility of the two resulting blockchains, leading to the devaluation of the associated cryptocurrency. It is worth noting that that a hard fork brought about as part of a 51% attack will be more likely to succeed in getting the new rules adopted since a consensus will be reached more easily.
- Money laundering: Blockchains are transparent by their very nature but the traceability of transactions can be made very complicated, which facilitates money laundering. It is possible to open a large number of accounts, use the accounts just once, and carry out transactions under the cover of a pseudonym. This raises questions about all of a blockchain’s contributors, since their moral values are essential to running the blockchain, and harms the technology’s image.
- Programming errors: Errors can be made in smart contracts, the programs that are automatically executed within a blockchain, and can have a dramatic impact on industrial players. Due to one such error an attacker was able to steal $50 million US from the DAO organization in 2016. Organizations who fall victim to such bugs could seek to invalidate these harmful transactions – the DAO succeeded in provoking a hard fork for this purpose — calling into question the very principle of the inalterability of the blockchain. Indeed, if blocks that have previously been recorded as valid in a blockchain are then made invalid, this raises questions about the blockchain’s reliability.
To conclude, the blockchain is a very promising technology that offers many characteristics to guarantee trust, but the problem lies in the disconnect between the promises of the technology and the ways in which it is used. This leads to a great deal of confusion and misunderstandings about the technology, which we have tried to clear up in this article.
Maryline Laurent, Professor and Head of the R3S Team at the CNRS SAMOVAR Laboratory, Télécom SudParis – Institut Mines-Télécom, Université Paris-Saclay
The original version of this article (in French) was published in French on The Conversation France.
Also read on I’MTech







Leave a Reply
Want to join the discussion?Feel free to contribute!